You should receive an email
with the registration link shortly.
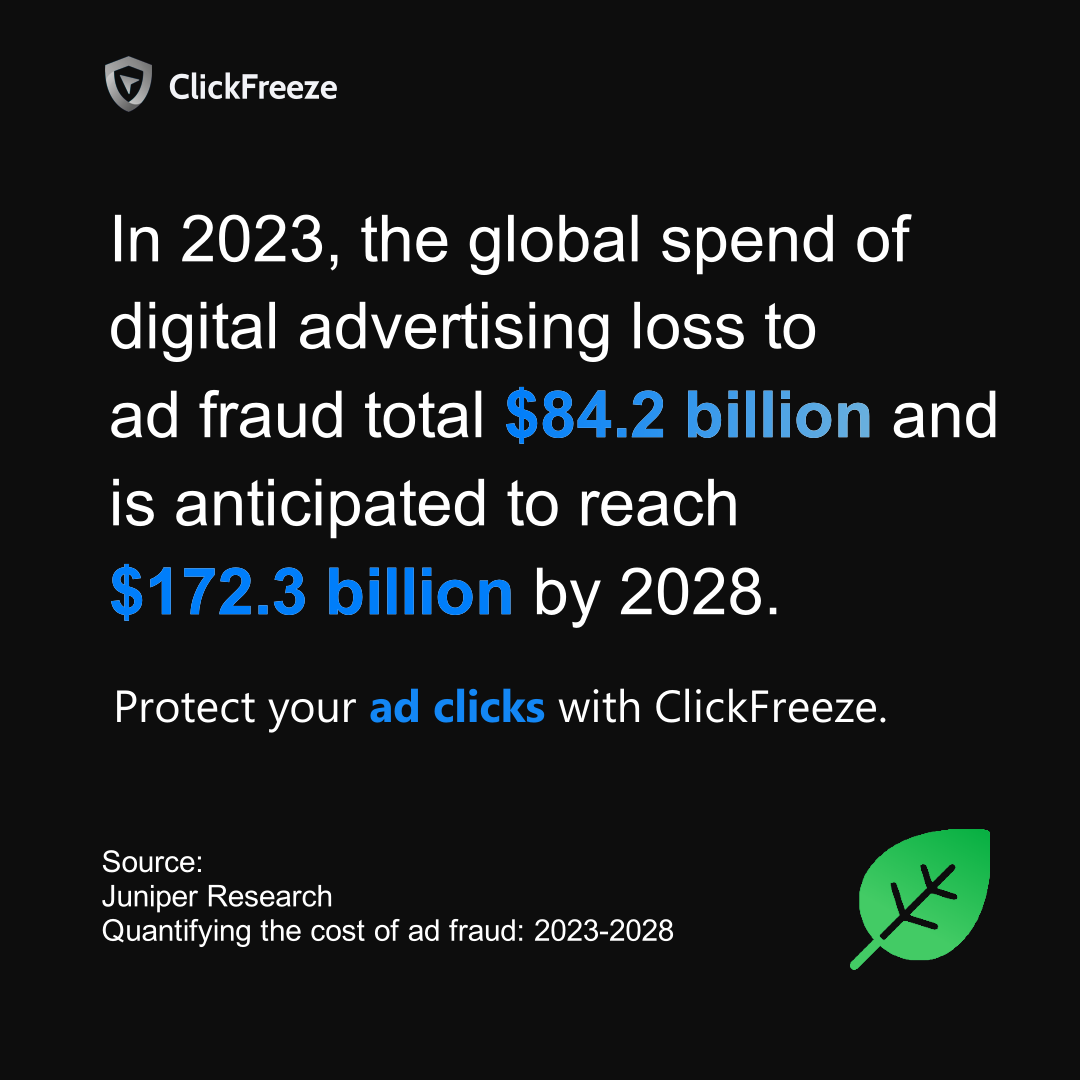 statistic
study
fraud
ads
statistic
study
fraud
ads
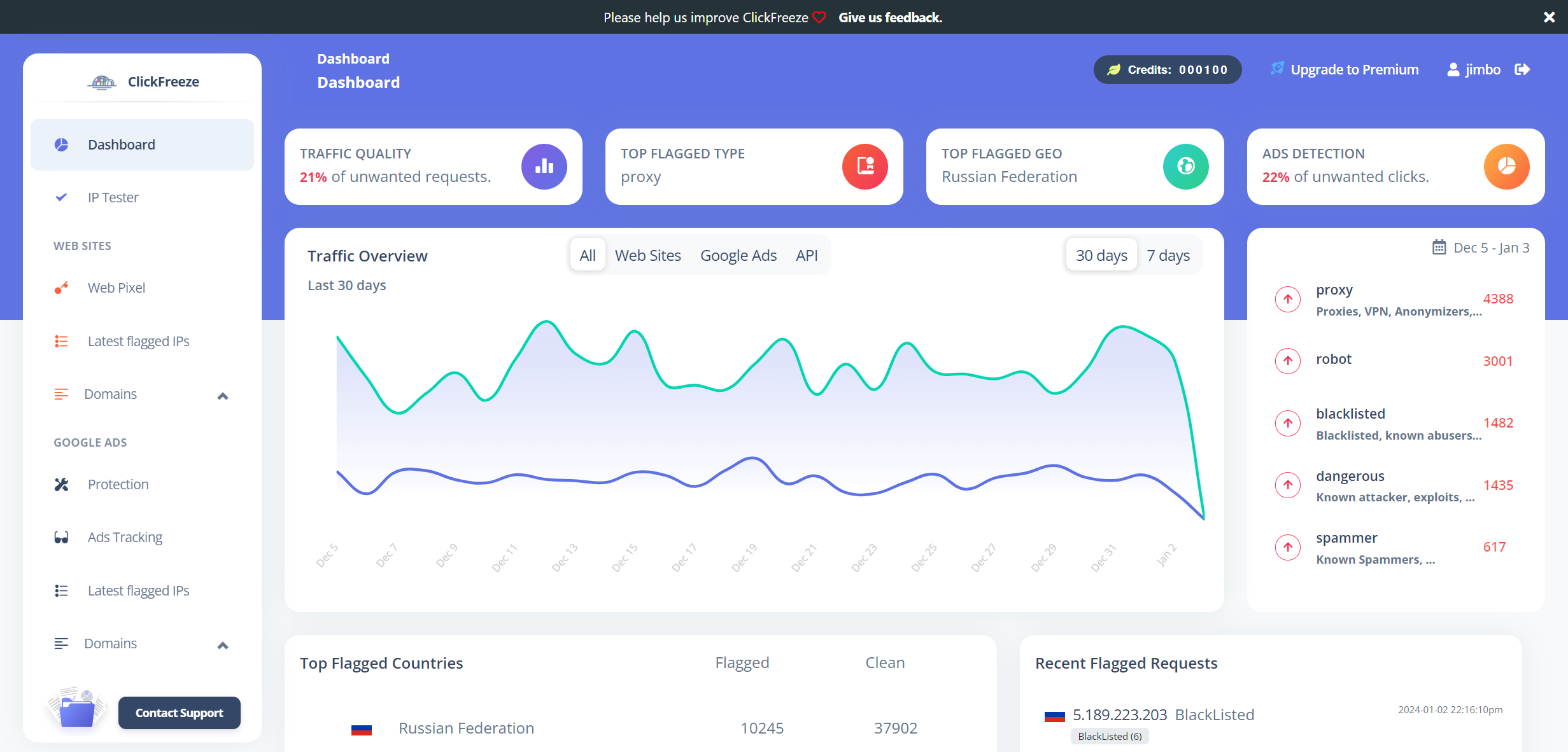
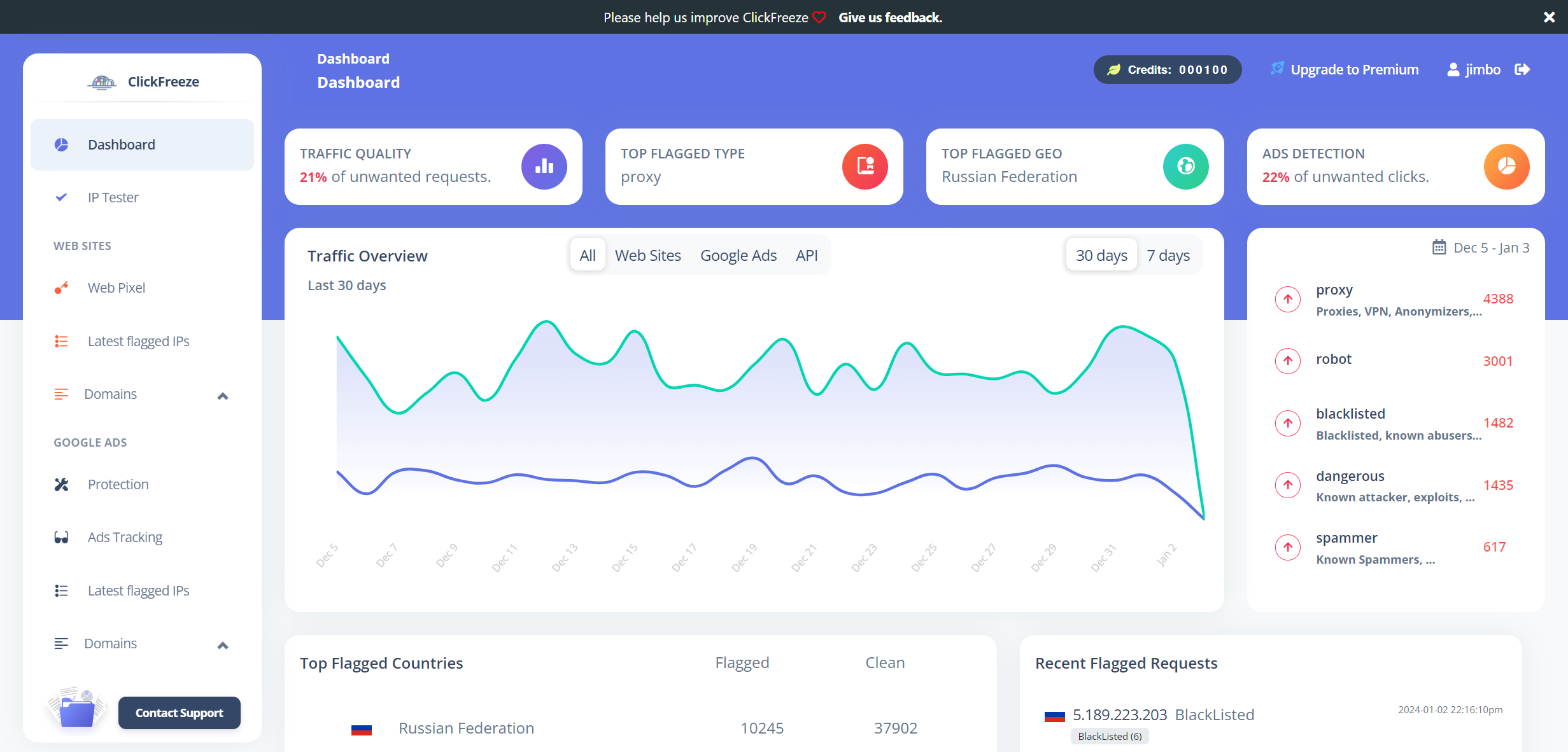
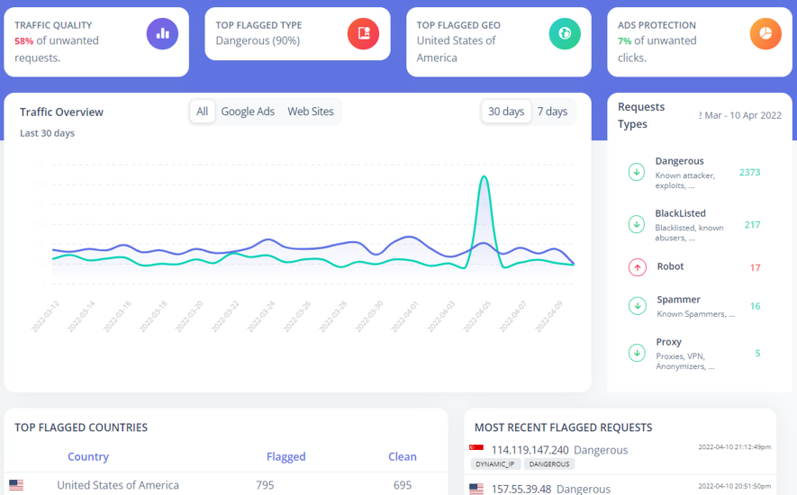
Modular design gives Web site and campaign managers the ability to see a status summary of their campaigns in real time.
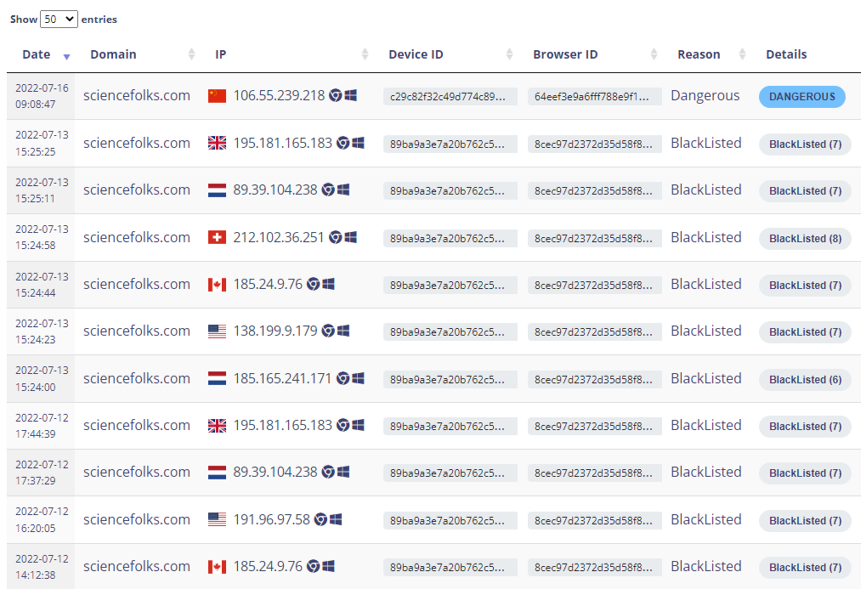
Calculated hardware devices signature and browser IDs, associated with our custom data, allows us to identify robots and fake users regardles of their location.
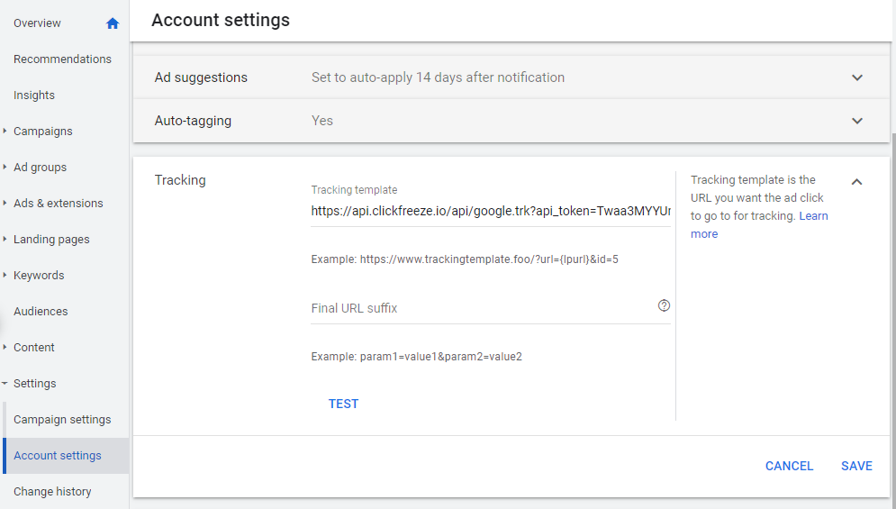
Google is one of the most used platforms for ADs, our system connects to your Google accounts to monitor and protects your campaigns.
Register today and stop wasting your budget.